Configure Google Single Sign-On in the Back-Office
Oro application supports Google Single Sign-On. This means that for a user that has the same primary email in the Oro application and Google accounts, it is enough to log in only once during a session.
Google Side
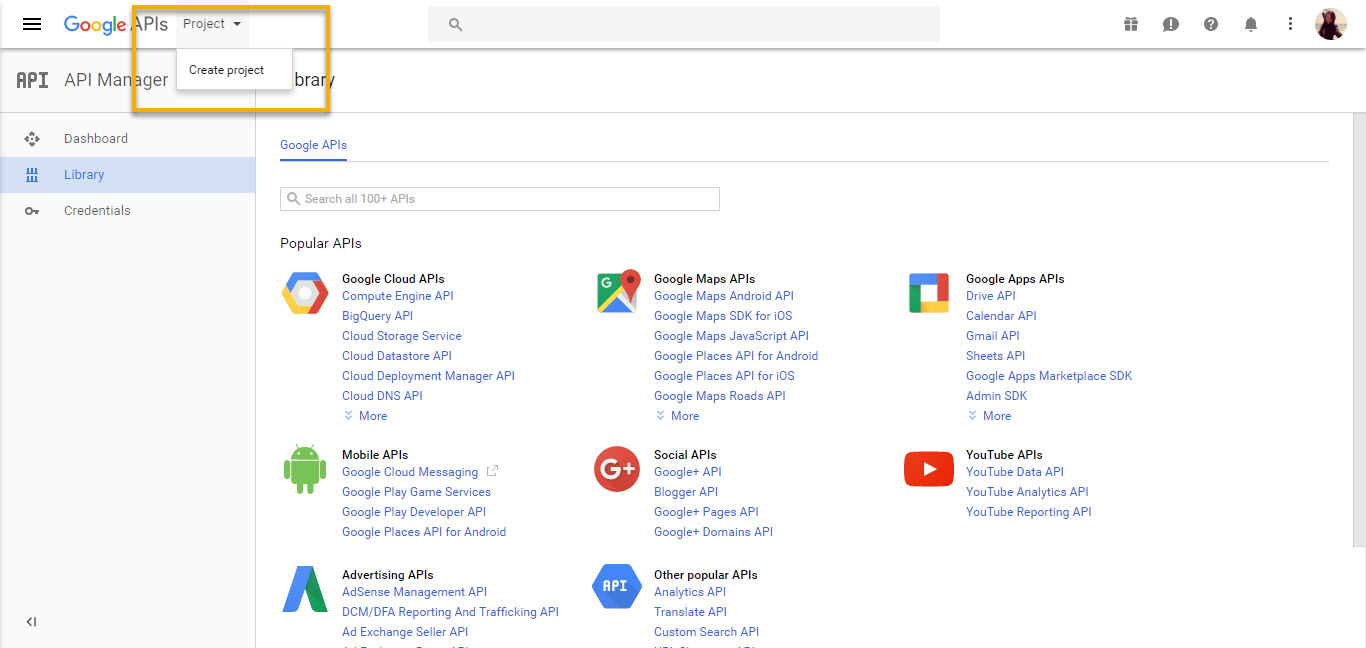
Create Project
To configure single sign-on on the Google side:
Open Google API Console.
Navigate to My Project selector in the top left corner and click Create Project.
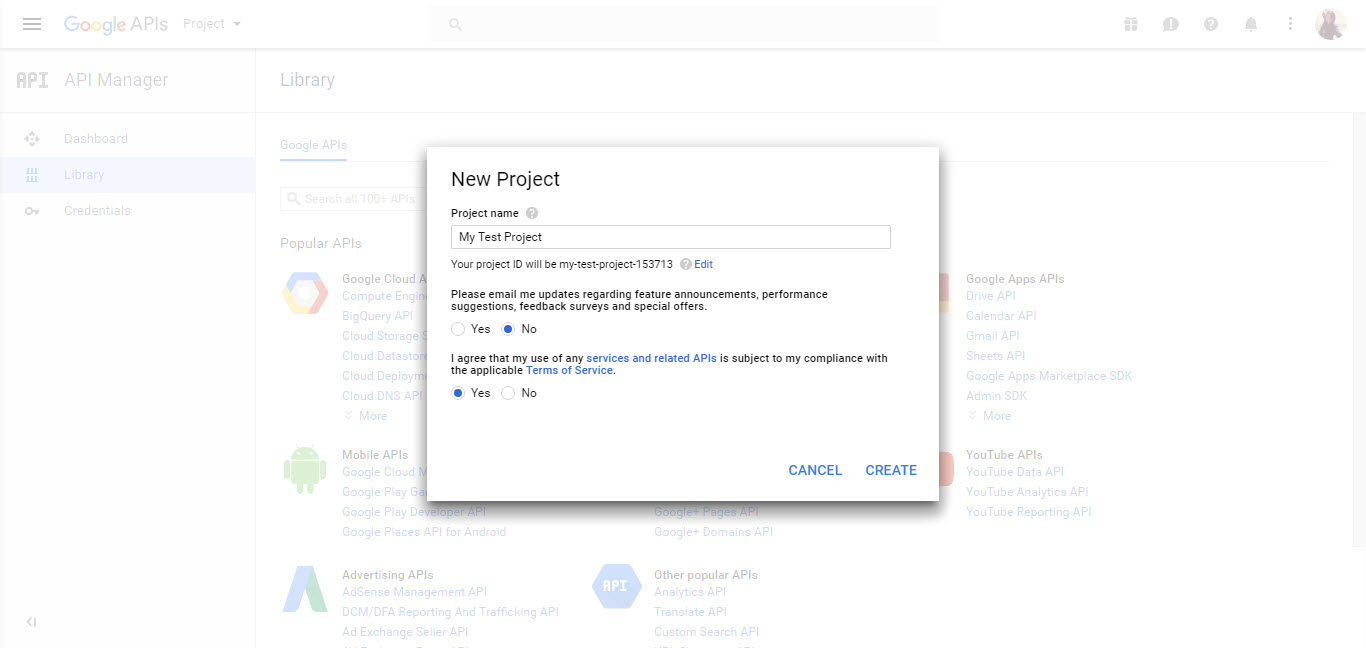
Define the Project Name and click Create.
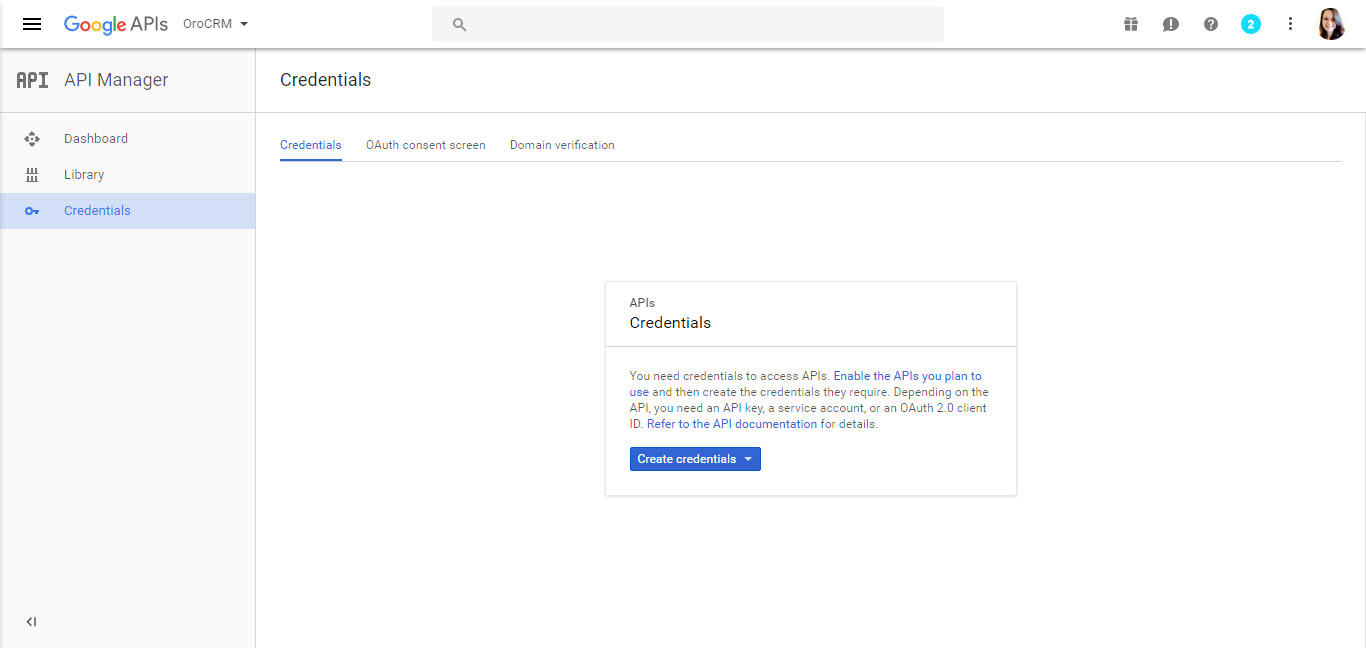
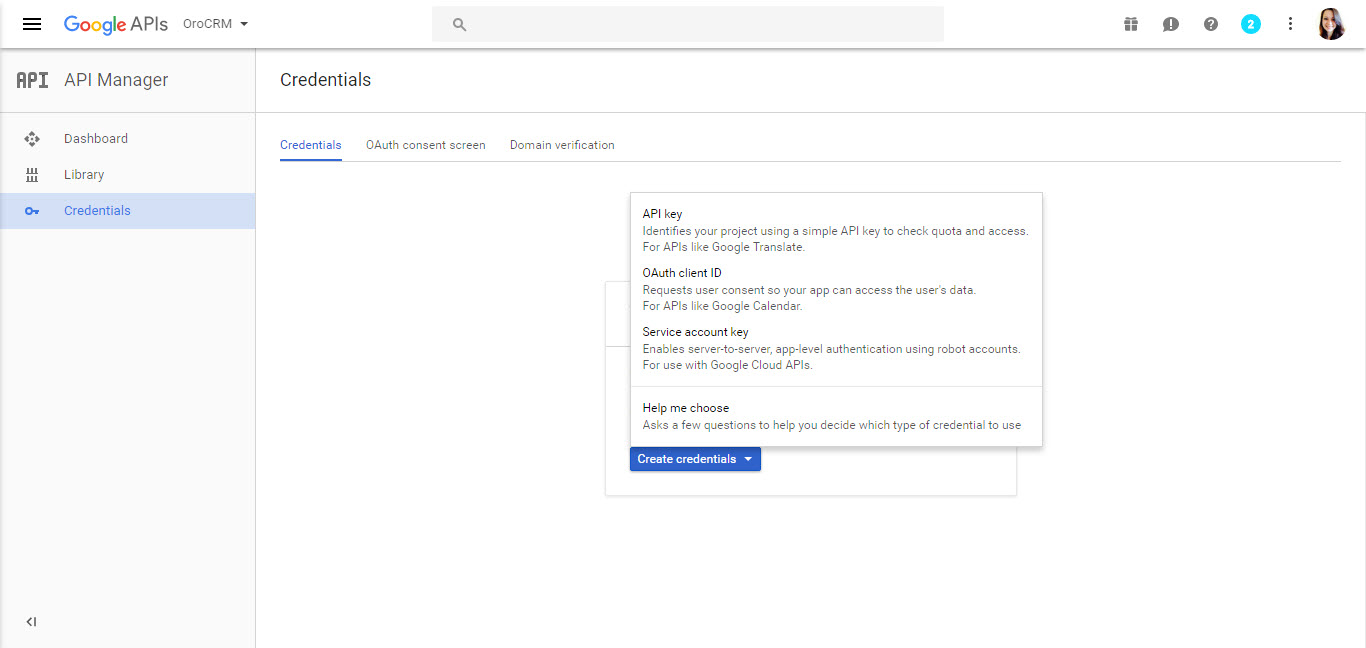
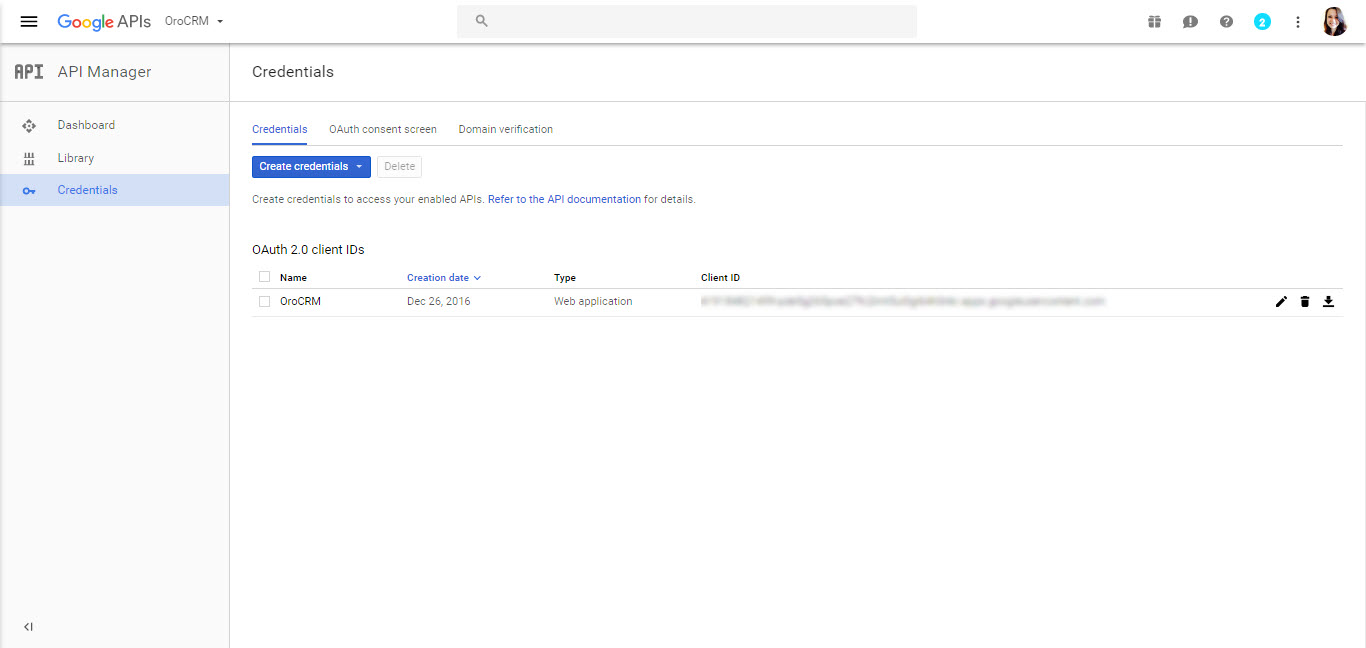
Create Credentials
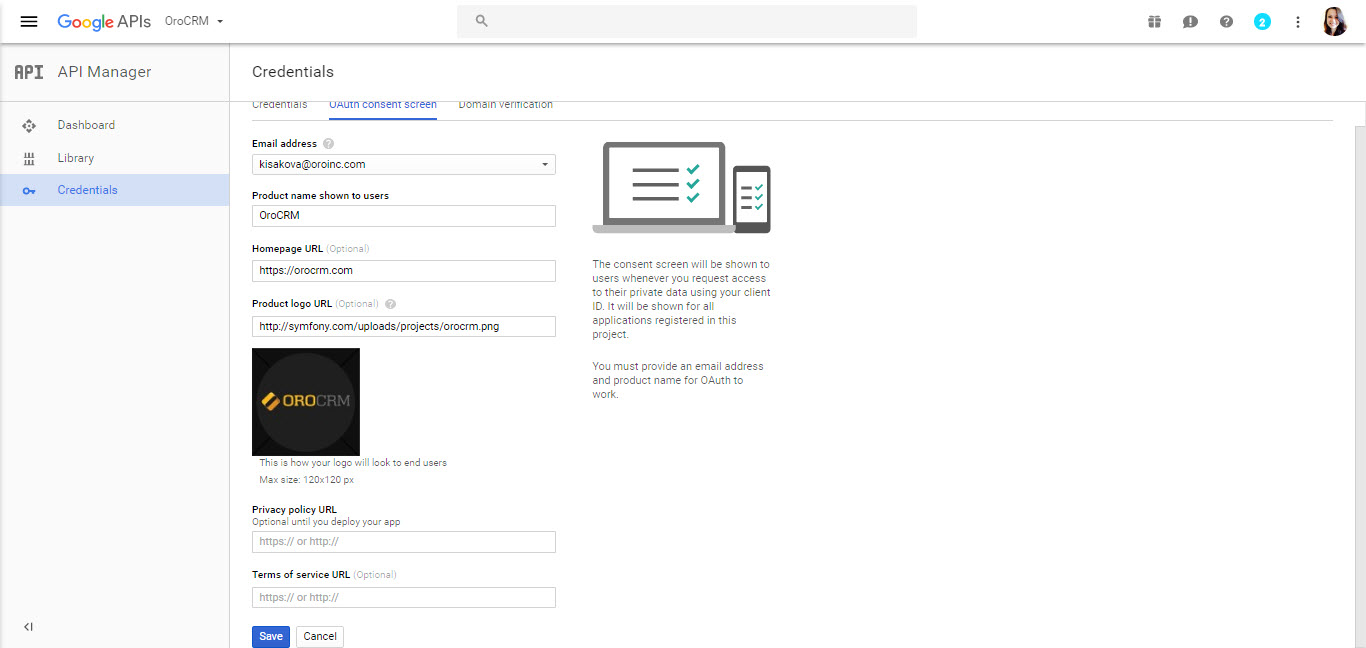
Configure Consent Form
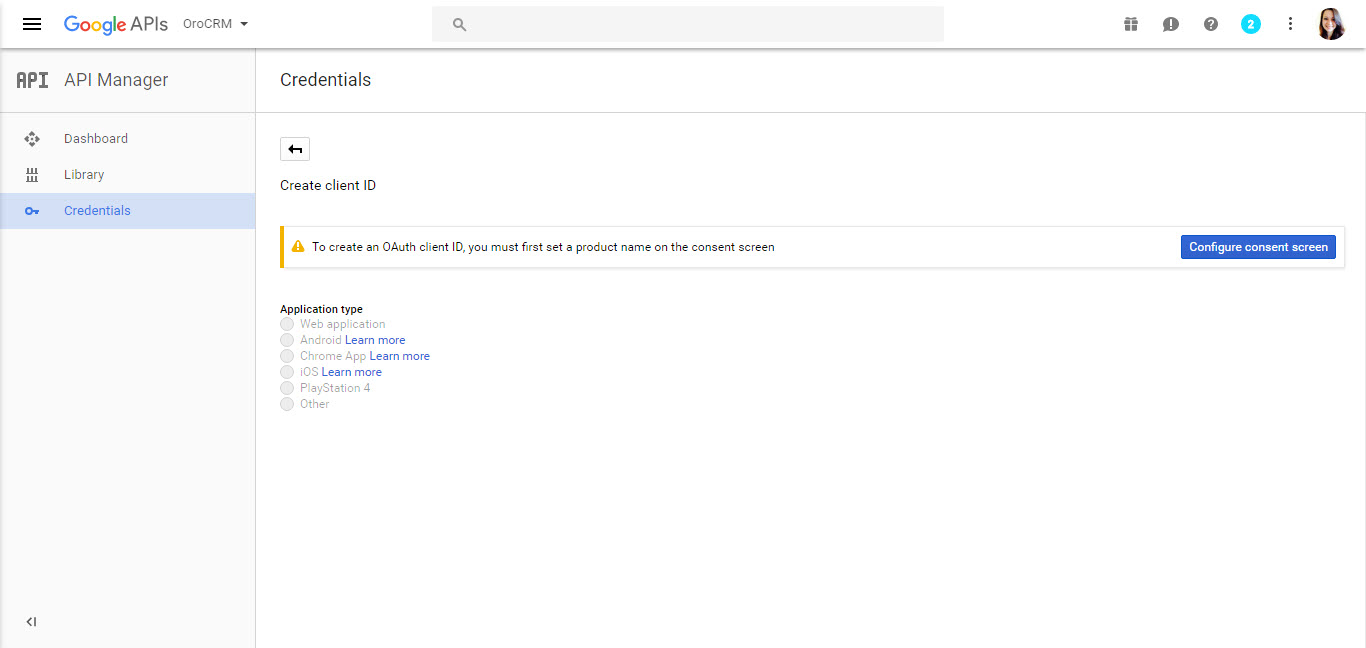
Click Save to launch the Create Client ID page.
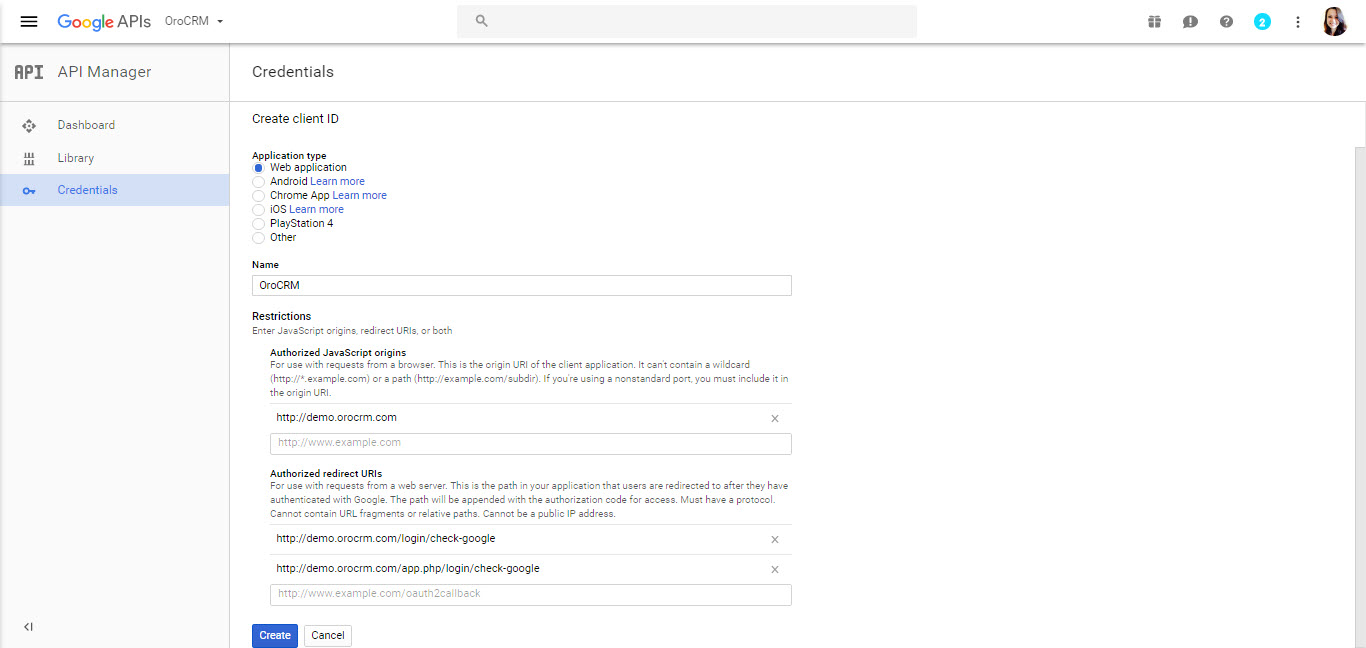
Set the Application Type to Web Application.
For Authorized JavaScript Origins, enter the URL of the Oro application instance for which single sign-on is being enabled.
Authorized Redirect URIs are unified resource names used for the interaction between Google and the Oro application instance. It is recommended to add the following two values:
[Oro application instance URL]/admin/login/check-google
[Oro application instance URL]/index.php/admin/login/check-google
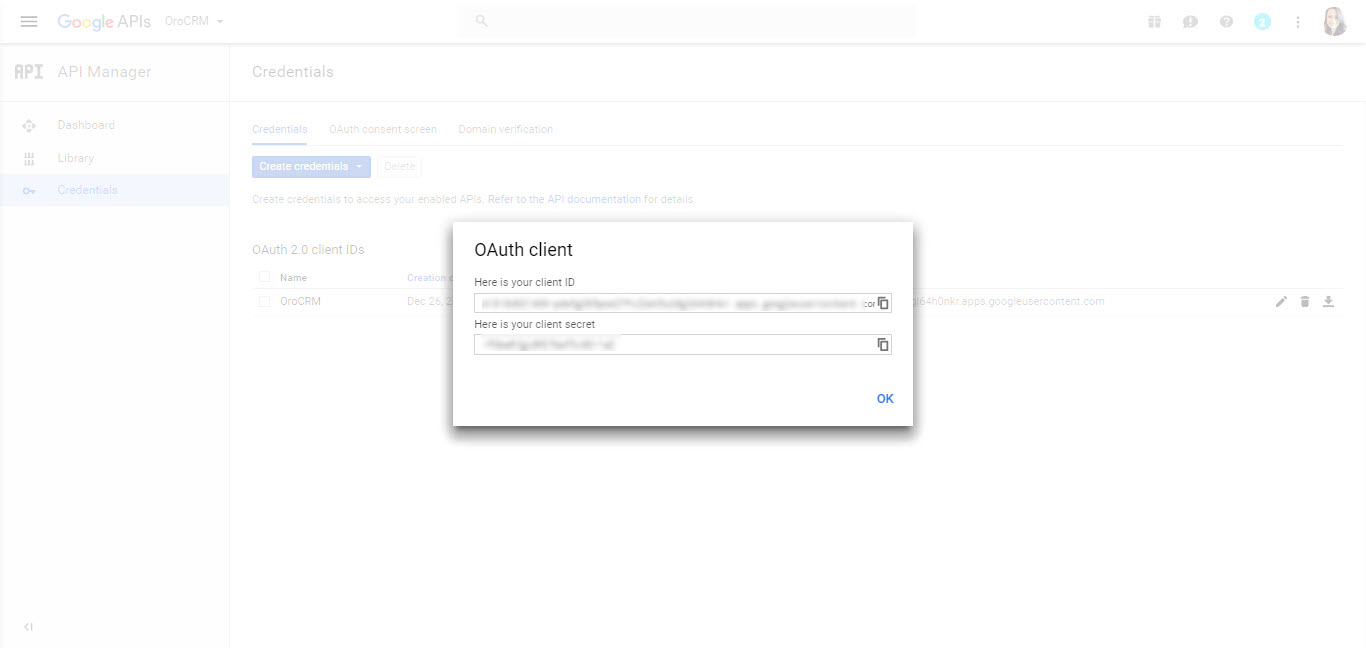
Click Create Client ID.
Note
Please pay attention to the Authorized Redirect URIs, the value from the System > Configuration > Integrations > Google Settings > Google Integration Settings > Redirect URI must be added in Authorized Redirect URIs configuration.
Oro Application Side
Configure Google Single Sign-On
To configure the integration with Google Single Sign-On in your Oro application:
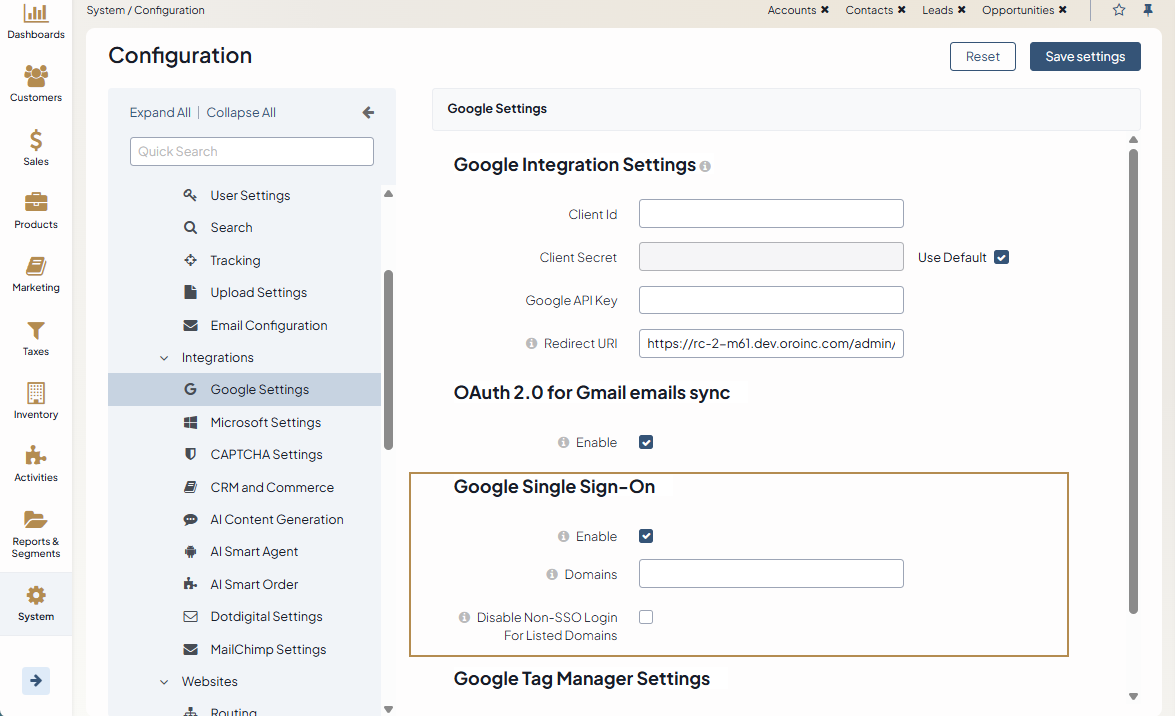
Navigate to System > Configuration > Integrations > Google Settings in the main menu.
Make sure that the information in the Google Integration Settings and OAuth 2.0 for Gmail emails sync is filled as described in the Configure Google Integration Settings topic.
Define the following fields for Google Sign-on:
Enable — Check Enable to activate Google Single Sign-on.
Domains — Domains is a comma separated list of allowed domains. It limits the list of mailboxes for which single sign-on can be used (e.g., only a domain used specifically by your company). Leave the field empty to set no such limitation
Log in with Google
When a user opens the login page of the instance with the enabled single sign-on capability, the Login Using Google link is displayed.
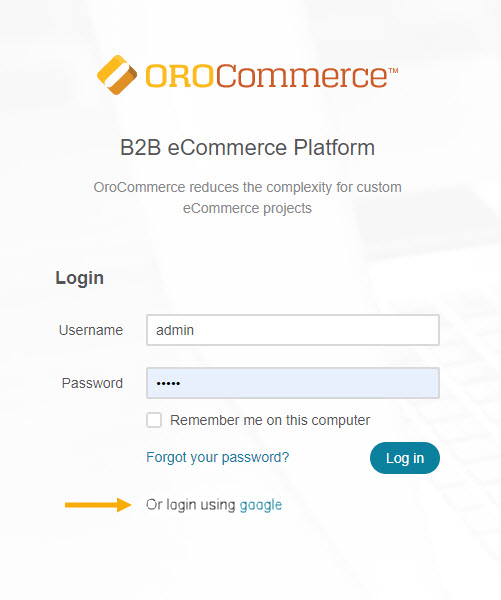
If the user is not logged into their Google account, then clicking the button triggers opening a usual Google login page.
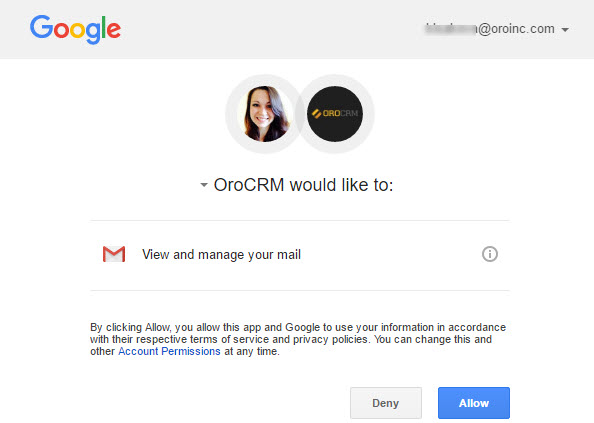
As soon as the user logs into their Google account, they need to accept the policy of using the application.
As soon as the user has logged into their Google account, a request to use the account in order to login to the Oro application is displayed (details defined for the consent screen is used).
Now, a Google-registered user can click the Login using Google button to enter the Oro application.
Note
Note that the email used for the Google account and the primary email of the user in the Oro application must be the same.
Related Topics